Vulnerability Management Process Template
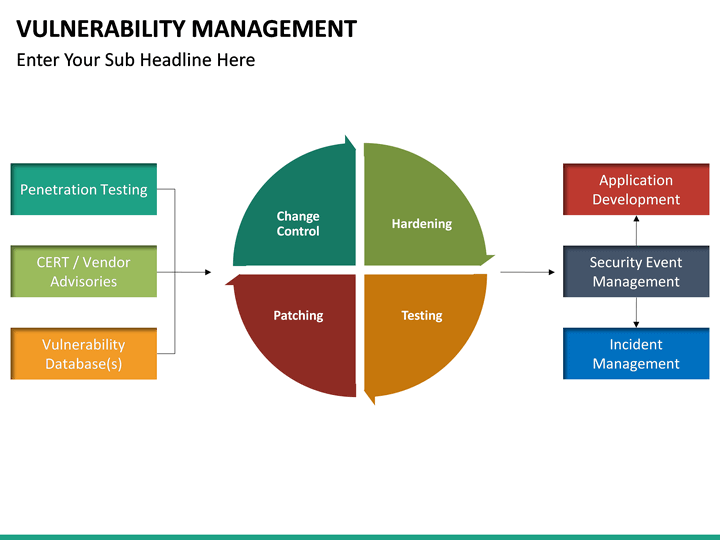
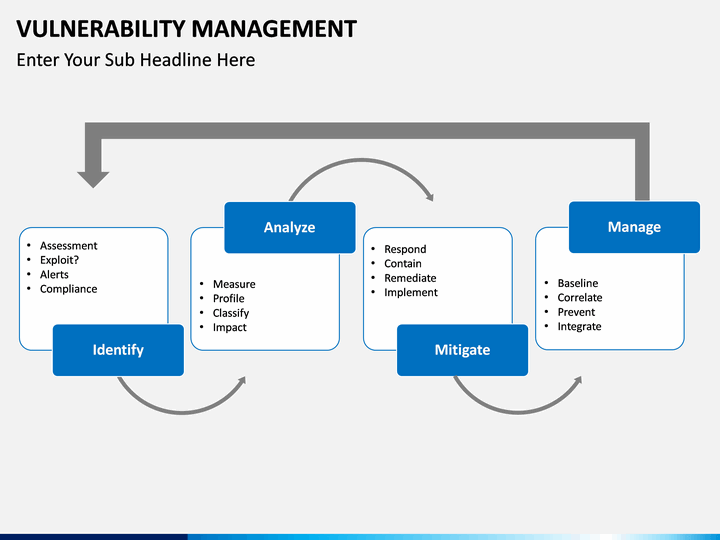
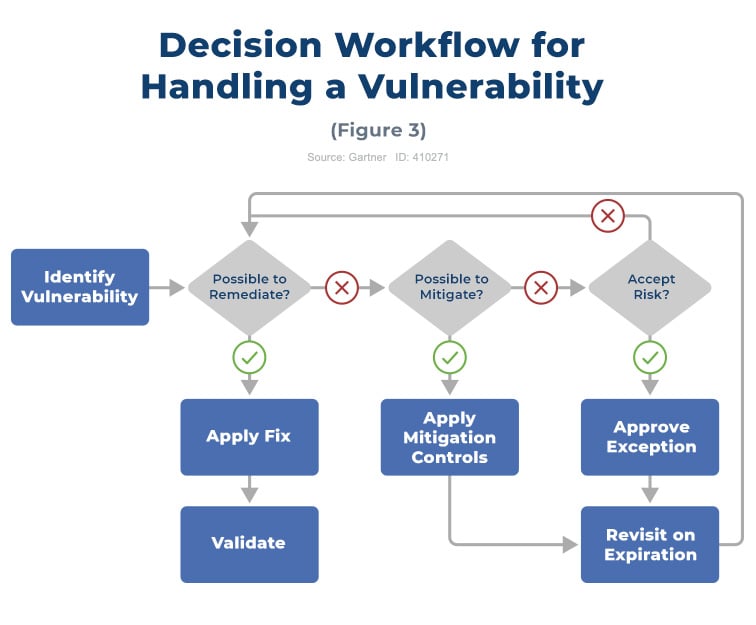
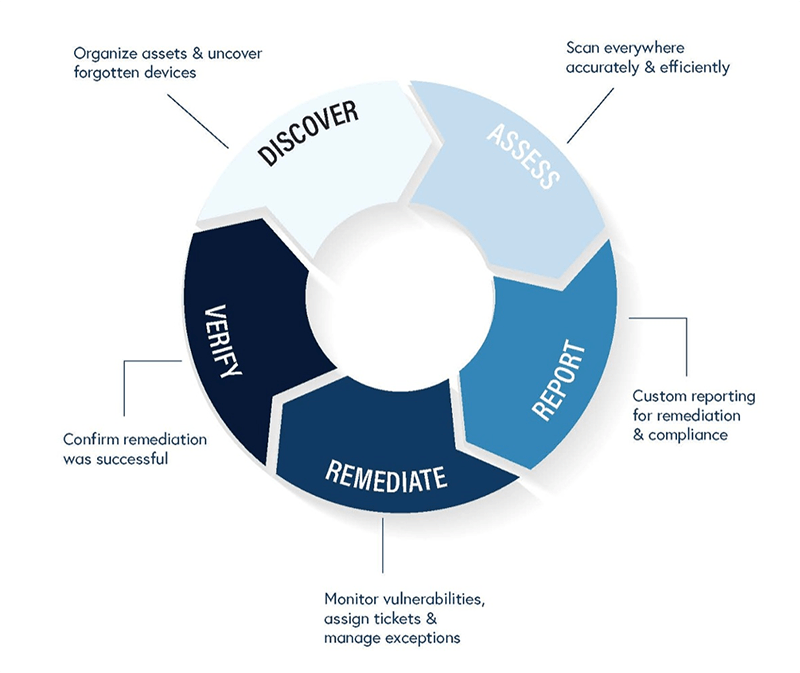
Vulnerability Management Process Template - Web 4 steps of the vulnerability management process. Web this guide is intended for organizations seeking help in establishing a vulnerability management process. Web vulnerability management resources. Web the vulnerability management process. Web download our free vulnerability management policy template now. Because new vulnerabilities can arise at any time, security teams approach. Stay current with free resources focused on vulnerability management. Web vulnerability management is a continuous, proactive, and often automated process that keeps your computer systems, networks,. Monitor public and private industry sources for new threat and vulnerability information. Web overview develop a plan to continuously assess and track vulnerabilities on all enterprise assets within the enterprise’s infrastructure, in order to remediate, and minimize, the window of opportunity for attackers. Web download our free vulnerability management policy template now. Guide the recruiter to the conclusion that you are the best candidate for the vulnerability. Web vulnerability management is one of the most effective means of controlling cybersecurity risk. Stay current with free resources focused on vulnerability management. Web vulnerability management is a continuous, proactive, and often automated process that keeps. You can export it in multiple formats like jpeg, png and svg and. Web this guide is intended for organizations seeking help in establishing a vulnerability management process. Web guidance to help organisations assess and prioritise vulnerabilities. Monitor public and private industry sources for new threat and vulnerability information. Web the vmt coordinator should use the template below. Web vulnerability management resources. Web 4 steps of the vulnerability management process. Web overview develop a plan to continuously assess and track vulnerabilities on all enterprise assets within the enterprise’s infrastructure, in order to remediate, and minimize, the window of opportunity for attackers. Yet, as indicated by the wave of massive data breaches. Because new vulnerabilities can arise at any. Because new vulnerabilities can arise at any time, security teams approach. Web the vulnerability management process. Stay current with free resources focused on vulnerability management. Web vulnerability is defined in the iso 27002 standard as “a weakness of an asset or group of assets that can be exploited by. Web vulnerability management is a process organizations use to identify, analyze,. Web for example, the task “scope” feeds into multiple processes: Web definitions vulnerability scan: You can export it in multiple formats like jpeg, png and svg and. Download template purpose the purpose of the. Stay current with free resources focused on vulnerability management. Web definitions vulnerability scan: Monitor public and private industry sources for new threat and vulnerability information. Web this guide is intended for organizations seeking help in establishing a vulnerability management process. Web creating and implementing an vulnerability management policies and procedures is a vital component of any company’s cyber. Web the vmt coordinator should use the template below. Web vulnerability management is a continuous, proactive, and often automated process that keeps your computer systems, networks,. Web definitions vulnerability scan: The purpose of this procedure is to outline the steps in it vulnerability management adhering to the vulnerability. Web this paper looks at how a vulnerability management (vm) process could be designed and implemented within. Web vulnerability management is. Web vulnerability management is a process organizations use to identify, analyze, and manage vulnerabilities within. The purpose of this procedure is to outline the steps in it vulnerability management adhering to the vulnerability. Web the guide to resume tailoring. Web 4 steps of the vulnerability management process. Cis controls v8 and resources An automated tool used to detect security weaknesses in a system or network. Web the vmt coordinator should use the template below. Monitor public and private industry sources for new threat and vulnerability information. Stay current with free resources focused on vulnerability management. Guide the recruiter to the conclusion that you are the best candidate for the vulnerability. Web vulnerability management resources. Web for example, the task “scope” feeds into multiple processes: Web vulnerability management is a continuous, proactive, and often automated process that keeps your computer systems, networks,. Web creating and implementing an vulnerability management policies and procedures is a vital component of any company’s cyber. You can export it in multiple formats like jpeg, png and. Web the vulnerability management process. Overview 1.1 procedure owner 1.2 classification 1.3 applicable regulations 1.4 related [company]. Web vulnerability management is a process organizations use to identify, analyze, and manage vulnerabilities within. Web definitions vulnerability scan: Web 4 steps of the vulnerability management process. The purpose of this procedure is to outline the steps in it vulnerability management adhering to the vulnerability. An automated tool used to detect security weaknesses in a system or network. Guide the recruiter to the conclusion that you are the best candidate for the vulnerability. Web the guide to resume tailoring. Web this paper looks at how a vulnerability management (vm) process could be designed and implemented within. Web you can easily edit this template using creately. You can export it in multiple formats like jpeg, png and svg and. Cis controls v8 and resources Web overview develop a plan to continuously assess and track vulnerabilities on all enterprise assets within the enterprise’s infrastructure, in order to remediate, and minimize, the window of opportunity for attackers. Web guidance to help organisations assess and prioritise vulnerabilities. Web the vmt coordinator should use the template below. Web creating and implementing an vulnerability management policies and procedures is a vital component of any company’s cyber. Yet, as indicated by the wave of massive data breaches. Web use this tool in order to build out your vulnerability management mitigation process. Web vulnerability is defined in the iso 27002 standard as “a weakness of an asset or group of assets that can be exploited by.Vulnerability Management PowerPoint Template SketchBubble
Vulnerability Management PowerPoint Template SketchBubble
Vulnerability Management PowerPoint Template SketchBubble
Vulnerability Management PowerPoint Template SketchBubble
Vulnerability Management PowerPoint Template SketchBubble
Vulnerability Management PowerPoint Template SketchBubble
What Is Vulnerability Management? Get the Answers You Need
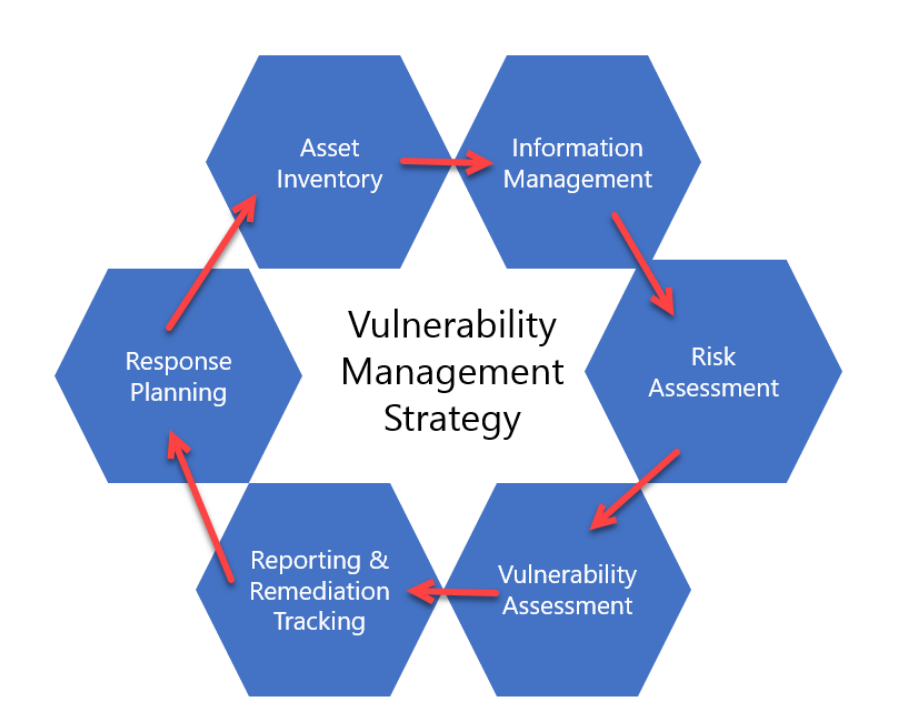
Creating a Vulnerability Management Strategy zSecurity
Vulnerability Management Act Stage
The Five Stages of Vulnerability Management
Related Post: